Course Design By
Nasscom & Wipro
Critically analyzing different techniques & effectiveness.
Demonstrating the use of tools in multiple remote devices.
Understanding the web attacks going through the process.
Applying out ethical theories on multiple technologies.
Compare & contrasting multiple proceedings.
Ethical Hacking has an infinite future that consists of many verticals like government, corporate enterprises as well as healthcare.
According to recent data, only 32% of people work in the Ethical Hacking industry as the demand for new staff rising simultaneously.
The credentials required for admittance get out approved as well as recognized out globally.
You can also apply for a global certification exam with the proper skill set.
Upon the completion of the course, you can be hired by top recruiters.
Let us see why Ethical Hacking Course in Gurgaon is so much appreciated by businesses and why to choose it as a career option. Here are some known facts for you.
Learning about ethical hacking involves studying the mindset & correcting the vulnerabilities going through the process.
The most obvious advantage of ethical hacking is to inform & improve corporate network gets defended.
The roles & responsibilities of ethical hackers & quality assurance need to overlap with each other.
A trained ethical hacker can be a major source for effectively managing multiple procedures.
It increases overall ROI and sales/marketing team efforts as well as updating business information.
Monitoring the IT (Information Technology) infrastructure for preventing real-time attacks.
Ensuring our subsequent analysis & investigation.
Evolving out security threats and handling client networks.
Usage of analytics software for fulfilling business needs.
Maintaining effective communication in the organization.
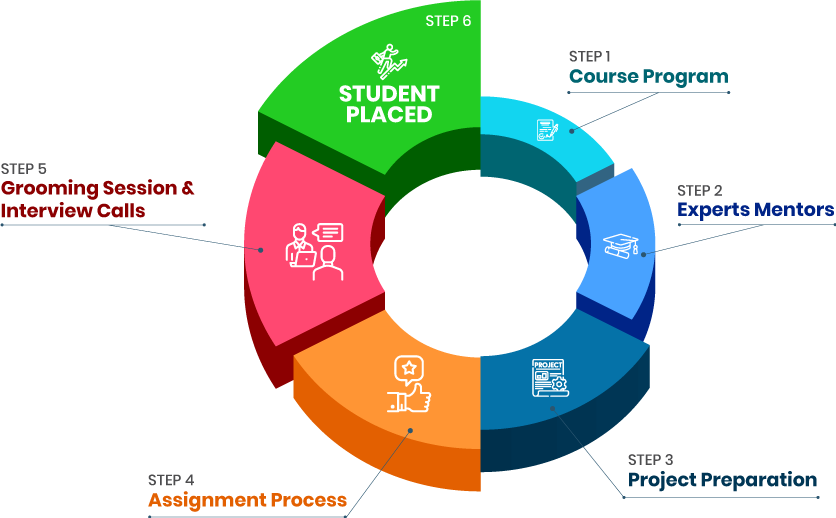
we train you to get hired.

By registering here, I agree to Croma Campus Terms & Conditions and Privacy Policy
+ More Lessons
Course Design By
Nasscom & Wipro
Course Offered By
Croma Campus
Stories
success
inspiration
career upgrade
career upgrade
career upgrade
career upgrade
You will get certificate after
completion of program
You will get certificate after
completion of program
You will get certificate after
completion of program
in Collaboration with

Empowering Learning Through Real Experiences and Innovation
we train you to get hired.
Phone (For Voice Call):
+91-971 152 6942WhatsApp (For Call & Chat):
+91-971 152 6942Get a peek through the entire curriculum designed that ensures Placement Guidance
Course Design By
Course Offered By
Ready to streamline Your Process? Submit Your batch request today!
Ethical Hackers can turn out unscrupulous use of information for executing malicious hacking activities.
JavaScript gets mostly used in programming languages.
HTML refers to Hyper Text Markup Language which helps out in effectively organizing our website architecture.
Ethical Hacking doesn’t require coding but it is difficult to proceed with complicated processes without coding.
It is important to learn programming to become a good hacker.
Croma Campus provides Best Ethical Hacking Training in Gurgaon as per the current industry standards. Our training programs will enable professionals to secure placements in MNCs.
Our strong associations with top organizations like HCL, Wipro, Dell, Birlasoft, TechMahindra, TCS, IBM, etc. makes us capable to place our students in top MNCs across the globe.
We provide video recording tutorials of the training sessions, so in case if the candidate missed any class, he/she can utilize those video tutorials. All our training programs are based on live industry projects. Live Project based training with trainers having 5 to 15 years of Industry Experience.
We provide free demo classes in form of online and offline classes that are tailored to provide a complete overview of the course before joining the training. These are guided by expert ethical Hackers and explain the importance of the Ethical hacking training institute in Gurgaon.
Highest Salary Offered
Average Salary Hike
Placed in MNC’s
Year’s in Training

fast-tracked into managerial careers.
Get inspired by their progress in the
Career Growth Report.
FOR QUERIES, FEEDBACK OR ASSISTANCE
Best of support with us
For Voice Call
+91-971 152 6942For Whatsapp Call & Chat
+91-9711526942